When you create an Azure Function it is protected, by default, with the API key security. So when you need to call that function then you simply attach the provided API key to the request. API key security works fine for many of the scenarios but what if you need user-based access to that Azure Function?
In this article, we’ll focus on how to enable the Azure Active Directory (AAD) authentication on Azure Function App so a user or group can have access to the functions by logging in with its Azure Active Directory account.
For the purpose of the demo, I’ve created the Azure Function App called funauthdemo on which we’ll set up the AAD authentication.
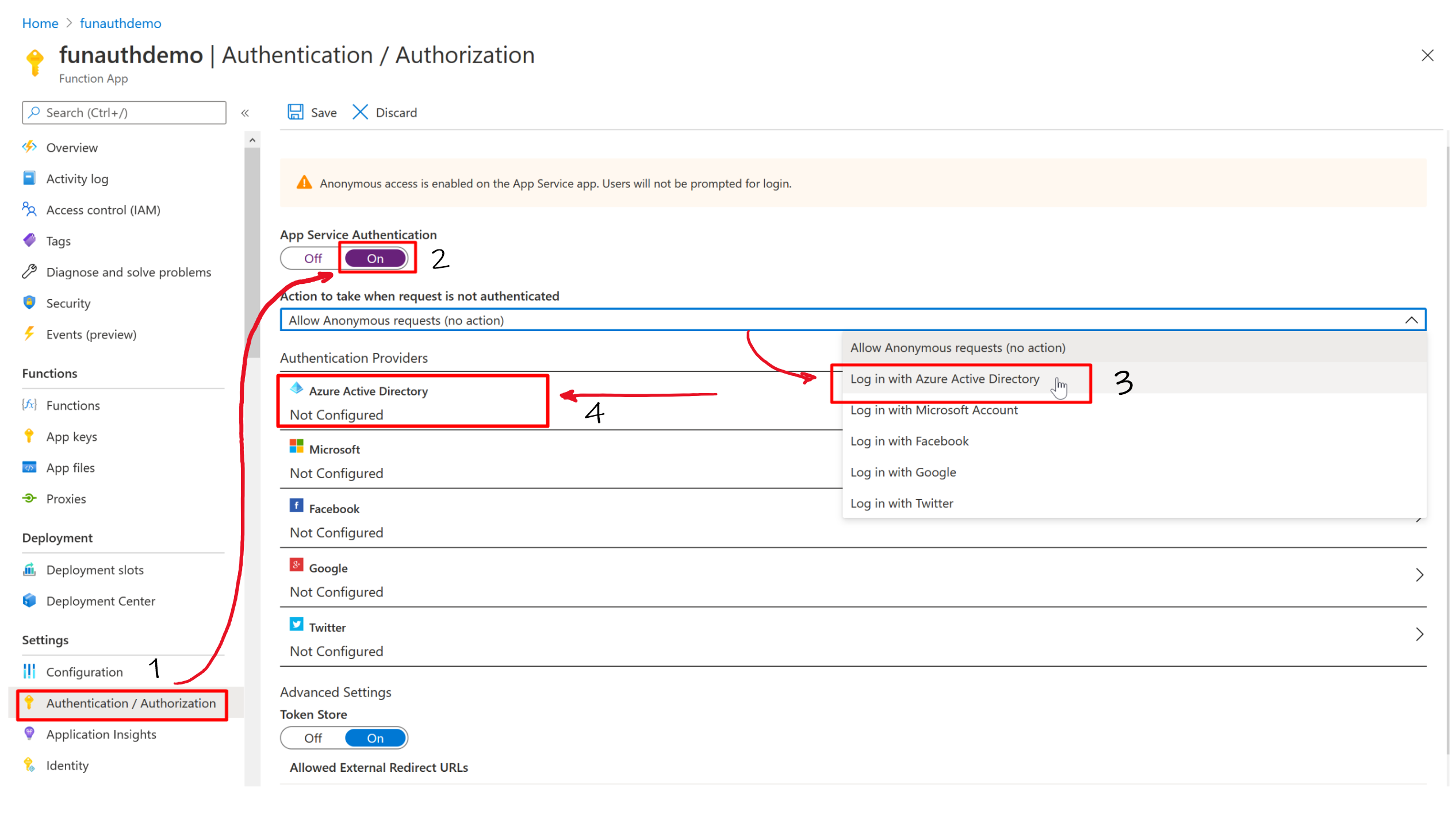
To enable AAD authentication on Function App, start with selecting Authentication / Authorization [1] and then turn On the App Service Authentication [2]. After that, we need to set what our Azure Function should do once it receives the unauthenticated request. From the menu “Action to take when the request is not authenticated” select “Log in with Azure Active Directory” [3].
As we are going to use the AAD authentication we need to configure the appropriate authenticated provider. So select from the list the “Azure Active Directory” provider [4].
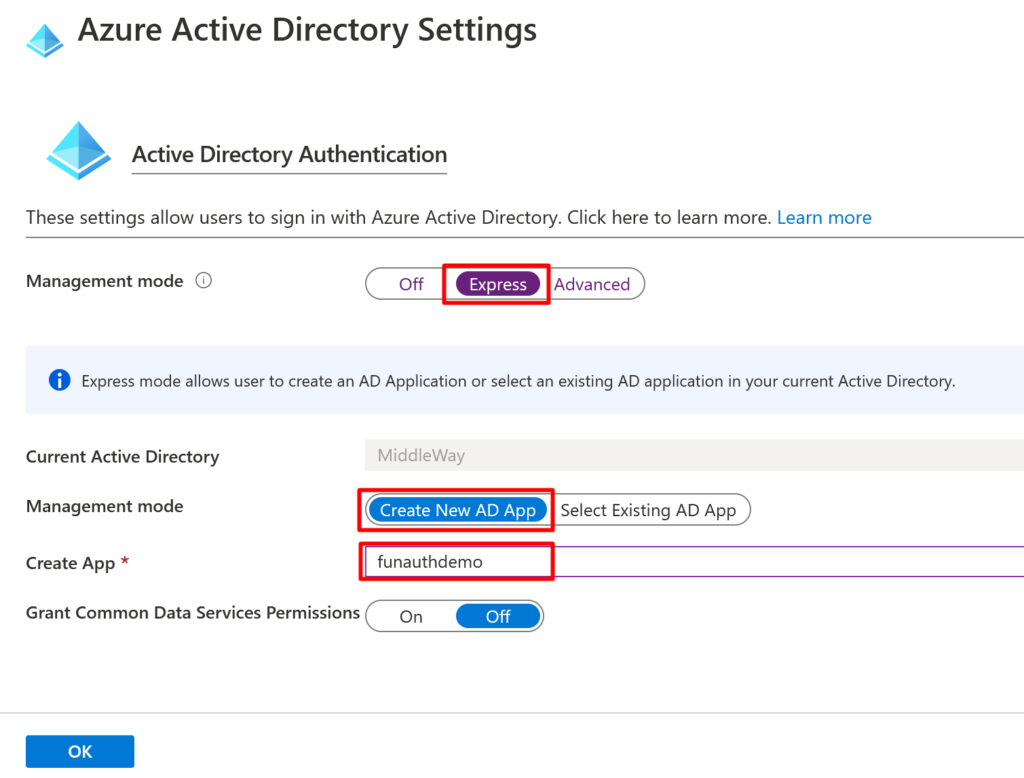
There two modes of Active Directory Authenticated settings – Express and Advanced. In our case we’ll choose the Express mode. If we’d like to use the Advanced management mode we should provide the ClientID (that we can find in App Registration blade) and issuer URL (https://sts.windows.net/<your_tenant_id>/).
To register our Function App in the Active Directory we can choose to Create a new Azure AD App or Select Existing AD App. Selecting the existing app could be useful for example in case we want to share the same AD identity configuration (e.g. same list of allowed users, etc) of the application already registered in the Active Directory. Well, in our demo, we’ll Create New AD App and we’ll called it funauthedemo.
Once everything is set, confirm the settings with the OK button.
After the settings are confirmed select Save to store the settings.
After the Authentication / Authorization settings are saved, the service principal is created in Azure Active Directory. So now our Function App is registered in AAD and we are able to do the authentication against the Active Directory.
More details on that Active Directory registration (such as ClientID, authentication tokens, user assignment, etc.) could be found in Application Registration and Enterprise Application blades of Azure Portal.
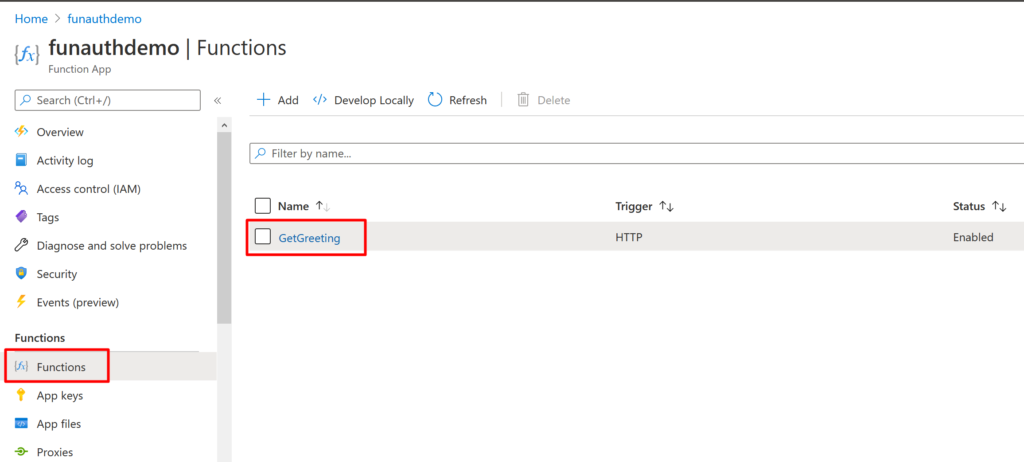
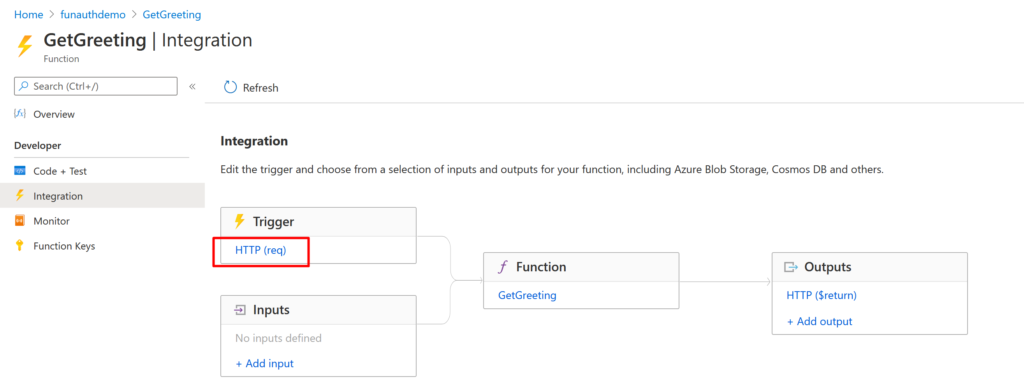
Now let’s create an Azure Function to Function App. I’ve created a simple HTTP trigger-based function called GetGreeting. The function should return the greeting message if we provide a value for the name parameter.
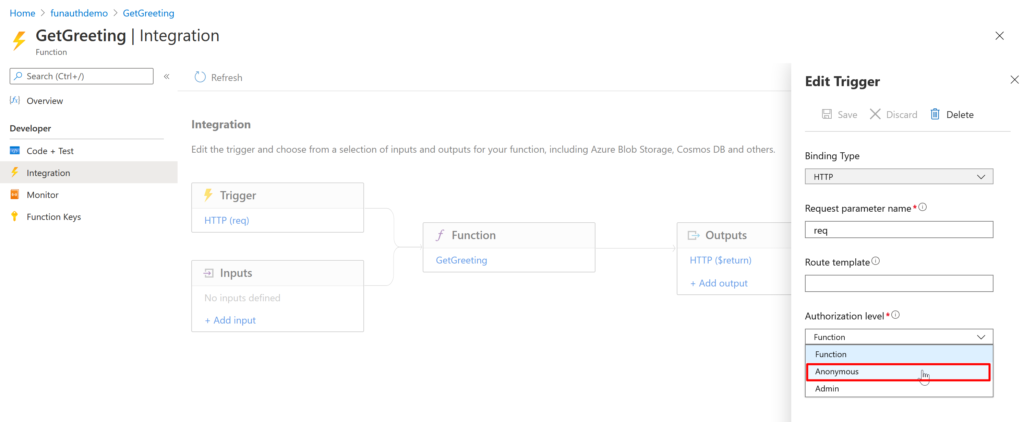
As we’ve already mentioned the Azure Functions are by default protected with API key. However, we’ve just enabled Active Directory authentication on the Function App and we do not want to use the API key. Therefore, to remove the API key security from the function, we should change the Authorization Level of the Azure Function from Function to Anonymous.
In the funauthdemo Function App, select the Functions menu and then open the GetGreeting function.
Then select the Integration to display the function trigger and the flow. Select HTTP (req) to open the trigger properties.
From the Authorization level menu select Anonymous and Save the trigger settings.
Now everything is ready to test the AAD authentication.
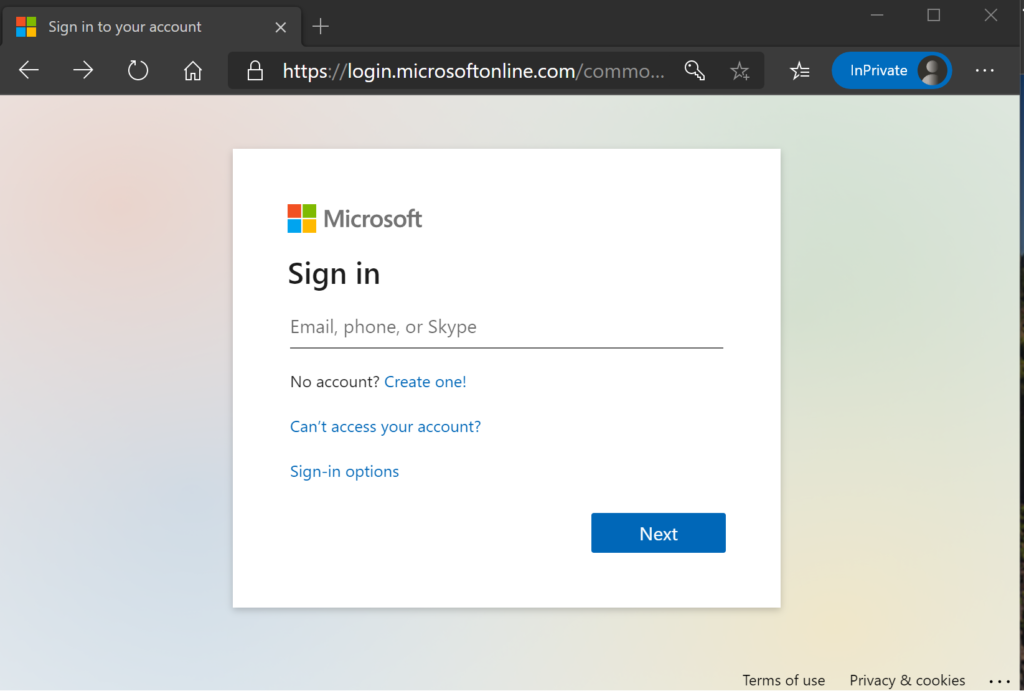
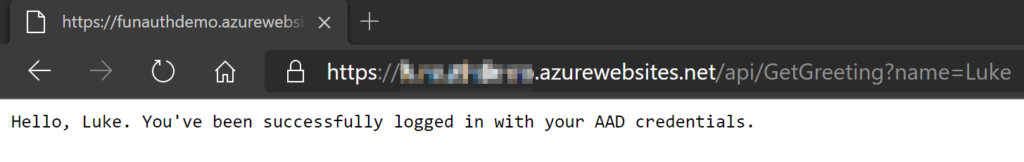
Firstly we need to get the function URL. Select Code + Test from the developer menu and then Get function URL (your URL will be something like https://your-function-app.azurewebsites.net/api/GetGreeting?name=Luke). Then open a browser with a private window and browse to the function URL. You’ll be prompted to provide the AAD credentials.
After the successful AD user authentication, the Azure Function is executed and provide us the following greeting:
We’ve seen in the article that setting up AD user authentication on Azure Function is quite straightforward and that the authentication: